48 CFR Mandates CMMC: Why Government Contractors Must Act Now

Cybersecurity has become a top national security concern. The U.S. Department of Defense (DoD) is no longer treating cyber compliance as optional or reactive. Through recent updates to the 48 Code of Federal Regulations (CFR), the government has now made it mandatory for defense contractors and subcontractors to comply with the Cybersecurity Maturity Model Certification (CMMC).
If your organization touches any part of the defense supply chain, now is the time to act. This article will break down what the 48 CFR changes mean, why CMMC is required, the risks of non-compliance, and how Techellence can help you prepare before it’s too late.
Why Cybersecurity Is a Contractual Priority
Cyberattacks on federal contractors have increased dramatically in recent years. From phishing to ransomware, the threats facing defense contractors aren't just technical—they're strategic. Bad actors target contractors because they are often the weakest link in national defense.
Sensitive but unclassified data, such as Controlled Unclassified Information (CUI) and Federal Contract Information (FCI), can reveal critical details about military operations, defense technologies, and infrastructure vulnerabilities. For this reason, the government now requires formal proof that contractors can safeguard this data.
What Changed in 48 CFR?
The 48 CFR is the backbone of how the U.S. federal government buys goods and services. It incorporates the Federal Acquisition Regulation (FAR) and the Defense Federal Acquisition Regulation Supplement (DFARS)—both of which define what contractors must do to qualify for and retain contracts.
Recent changes to DFARS and 48 CFR include language that makes CMMC certification a condition for contract eligibility. These updates are not just policy memos—they are legally enforceable requirements.
Here’s what the new mandate means:
-
Cybersecurity is no longer a checkbox. It is part of your contractual obligations.
-
Self-attestation is no longer sufficient. In many cases, contractors must pass a formal assessment.
-
Prime contractors are responsible for ensuring their subcontractors comply. This affects the entire supply chain.
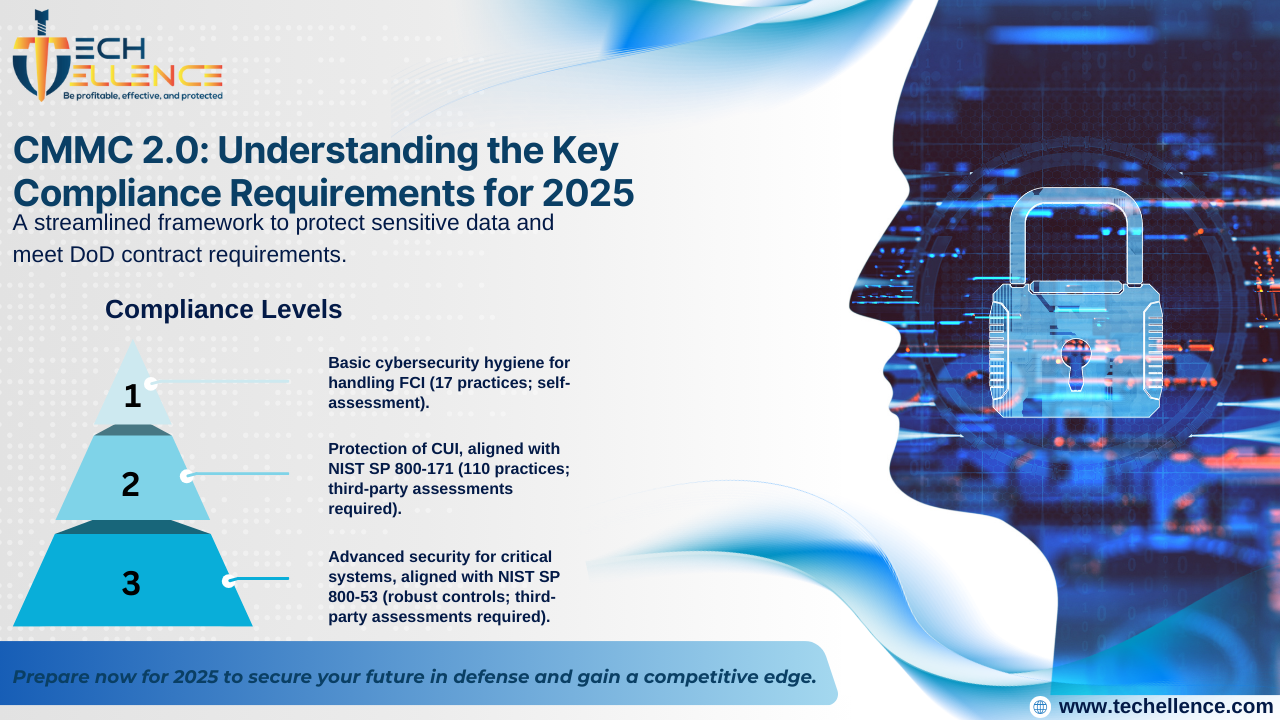
The Role of CMMC: From Guidance to Requirement
CMMC was developed to provide a structured and measurable framework for cybersecurity readiness in the defense industrial base (DIB). It builds on existing guidance—especially NIST SP 800-171, a widely used set of standards for protecting CUI in non-federal systems.
Under the CMMC framework, organizations must:
-
Document their security practices and policies
-
Demonstrate implementation of cybersecurity controls
-
Undergo audits or submit self-assessments, depending on the data they handle
-
Maintain compliance over time, not just at contract award
CMMC also emphasizes the importance of maturity and sustainability in cybersecurity. It’s not enough to have tools in place—your team must know how to use them, monitor their effectiveness, and respond to incidents effectively.
Real-World Impact: Why This Matters Now
The changes to 48 CFR and the rollout of CMMC into DoD contracts are already underway. The DoD has announced a phased implementation strategy where CMMC requirements will appear in select solicitations before becoming widespread.
That means:
-
Future solicitations may include CMMC as a prerequisite to even submit a proposal
-
Current contractors may be asked to show proof of compliance as contracts are renewed or modified
-
Organizations that ignore these requirements risk losing existing or upcoming business opportunities
Example scenario:
Imagine your company is a subcontractor providing parts for a defense aircraft system. If the prime contractor is required to show that everyone in their supply chain is CMMC compliant, and you are not, you could be replaced—regardless of past performance or cost.
Common Compliance Pitfalls
Many organizations misjudge what it takes to achieve compliance. Here are common mistakes:
-
Assuming IT staff can “handle it later” – Without leadership buy-in, compliance efforts stall.
-
Relying solely on software tools – Tools are helpful, but policies, procedures, and training are just as important.
-
Overestimating current security posture – Many organizations discover major gaps once they begin assessments.
-
Focusing only on passing an audit – CMMC is about ongoing security, not one-time certification.
Why Time Is a Critical Factor
Cybersecurity maturity doesn’t happen overnight. Becoming CMMC-ready may take 6 to 12 months or longer, depending on your current posture. If you wait until compliance is officially required in a contract, it may already be too late to compete.
Additional delays can occur if you:
-
Don’t have clear asset inventory
-
Lack formal documentation of policies
-
Have outdated or unpatched systems
-
Are unsure how data flows through your environment
-
Need to train your staff on compliance procedures
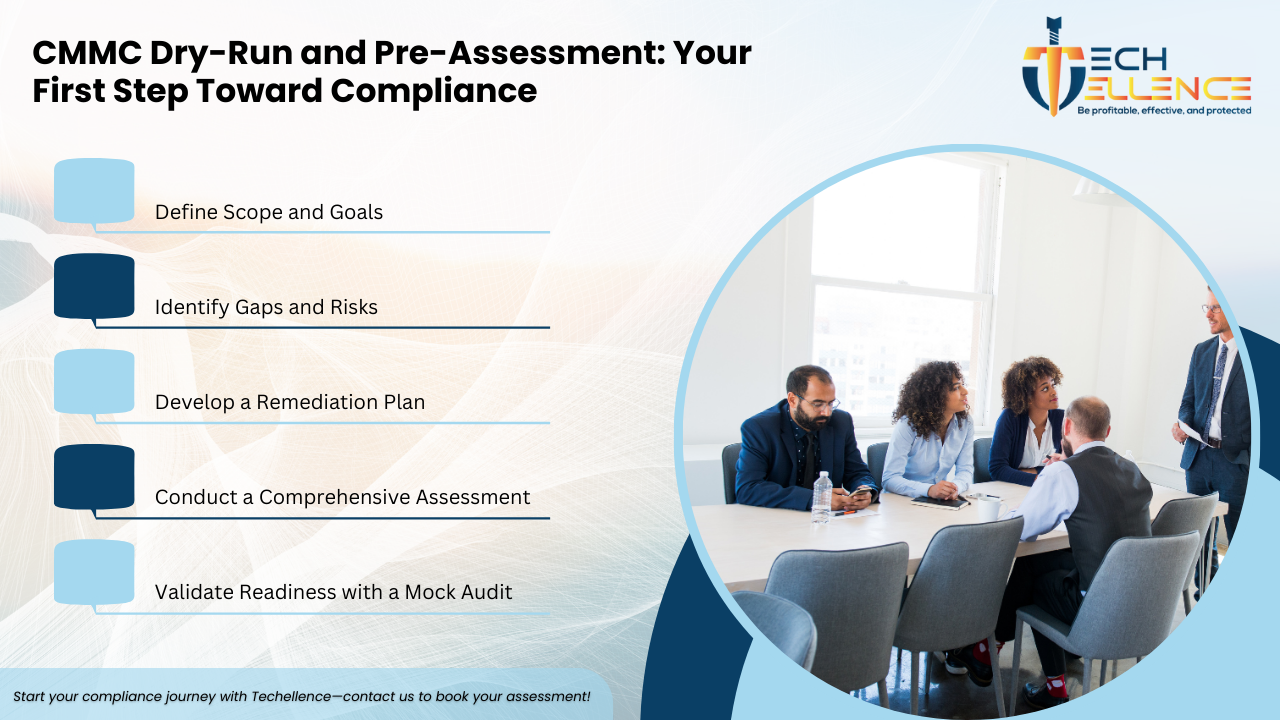
How Techellence Supports Your Compliance Journey
At Techellence, we partner with government contractors to build effective, sustainable, and auditable cybersecurity programs that align with CMMC and 48 CFR requirements. Our services are designed to meet you where you are—whether you’re just starting or already working toward certification.
Our CMMC Services Include:
-
CMMC Readiness Assessment
We evaluate your current cybersecurity practices against CMMC standards and provide a gap analysis. -
System Security Plan (SSP) and Plan of Action & Milestones (POA&M)
We help you develop required documentation that details your security policies and outlines how gaps will be addressed. -
Technical and Policy Implementation Support
From encryption to multi-factor authentication, we assist in implementing the right solutions tailored to your environment. -
Continuous Monitoring and Maintenance
Cybersecurity is not static. We offer ongoing support to ensure you stay compliant over time. -
Training and Awareness
We deliver customized employee training to strengthen your human firewall.
With Techellence, you're not just checking a box—you’re building a lasting defense.
Final Thoughts
CMMC’s inclusion in 48 CFR signals a broader shift in how the government manages cybersecurity risk. Contractors are now considered an extension of the federal defense perimeter. The cost of non-compliance is no longer theoretical—it’s contractual, financial, and reputational.
For businesses in the defense supply chain, acting now is not just a smart move—it’s essential for survival in a competitive, compliance-driven landscape.









.png)













.png)











.png)




.png)

.png)
.png)
.png)

