Preparing for a Joint Surveillance Voluntary Assessment (JSVA): What You Need to Know

For contractors supporting the U.S. Department of Defense, cybersecurity compliance is more than a regulatory requirement—it’s a business imperative. One proactive step organizations can take is to undergo a Joint Surveillance Voluntary Assessment (JSVA). This collaborative review helps you validate your cybersecurity posture before full certification requirements take effect.
Here’s what your organization needs to know to get ready.
What is a JSVA?
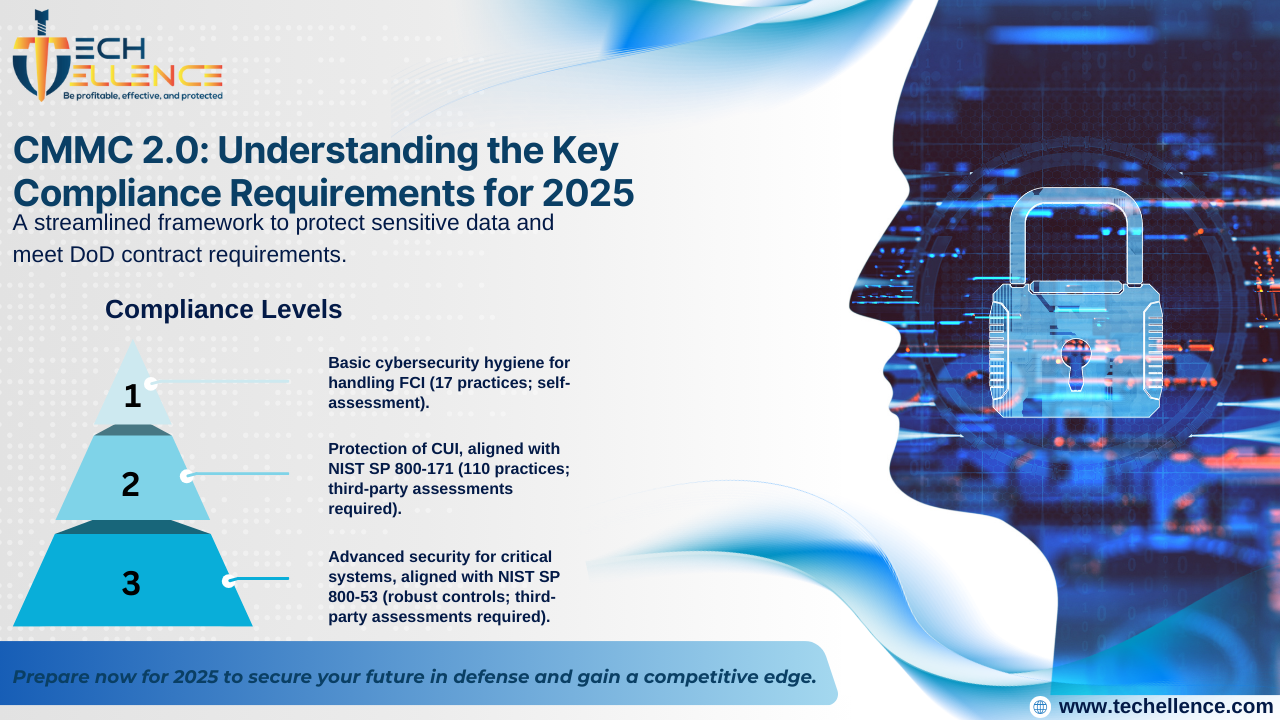
The Joint Surveillance Voluntary Assessment is a coordinated evaluation conducted by the Defense Industrial Base Cybersecurity Assessment Center (DIBCAC) together with a Certified Third-Party Assessment Organization (C3PAO). It follows the same standards used in formal Department of Defense (DoD) assessments and gives contractors a chance to verify that required cybersecurity practices are fully in place.
Why is it voluntary?
JSVA is designed as a transitional program. While not mandatory, it’s a strategic opportunity for organizations to:
-
Confirm that all required cybersecurity practices are implemented
-
Demonstrate commitment to safeguarding Controlled Unclassified Information (CUI)
-
Identify and address any compliance gaps early
-
Strengthen credibility with DoD and prime contractors
If your organization passes a JSVA, the results may be recognized by the DoD, saving time and effort down the road.
Key Preparation Areas
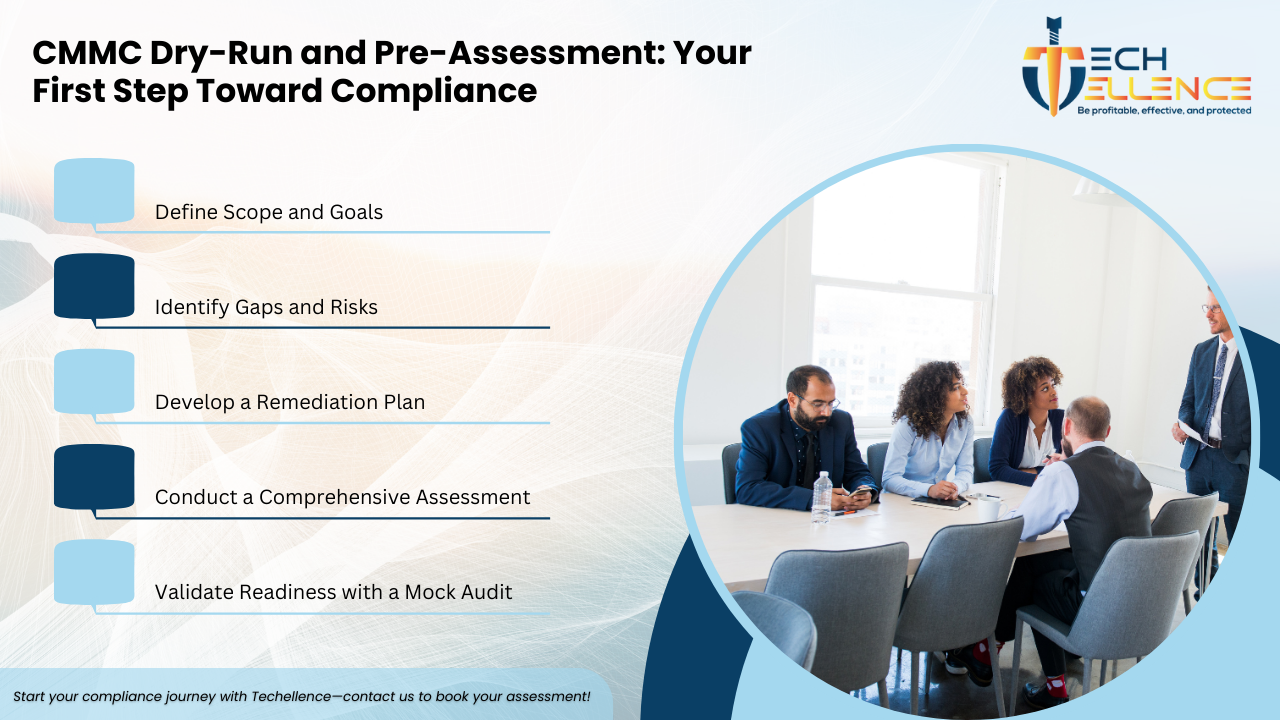
A successful JSVA requires more than just having policies in place. You must be able to demonstrate that your cybersecurity practices are well-documented, consistently applied, and measurable.
1. Document Your Cybersecurity Practices
Start with a complete and up-to-date System Security Plan (SSP). This should outline:
-
How each NIST SP 800-171 control is implemented
-
Network boundaries and data flow
-
Access control, encryption, and incident response mechanisms
Support your SSP with additional documentation such as diagrams, asset inventories, and system configurations.
2. Show Real Implementation
Auditors will expect to see real-world application—not just policies on paper. Be prepared to provide:
-
Evidence such as access logs, endpoint protection reports, and user training records
-
Demonstrations of tools and processes in action
-
Proof that your team follows the documented procedures
3. Train Your Team
Your staff should know their responsibilities in protecting CUI. Ensure they can confidently answer questions about their security roles and responsibilities. Consider running mock assessments to prepare.
4. Review and Remediate Gaps
Identify any missing or partially implemented practices and create a Plan of Action & Milestones (POA&M) to address them. Even though full implementation is required, having a clear remediation plan shows your commitment to security.
How Techellence Can Help
At Techellence, we support organizations throughout the JSVA preparation process. Our experienced team can:
-
Perform a readiness assessment based on NIST SP 800-171
-
Help develop and update your SSP and supporting documentation
-
Identify gaps and provide clear action plans
-
Guide your team through assessment expectations and evidence gathering
Whether you’re aiming for compliance or simply want to strengthen your cybersecurity, we can help you move forward with confidence.
Final Thoughts
The Joint Surveillance Voluntary Assessment is more than a review—it’s a strategic opportunity. Preparing now allows you to build a strong cybersecurity foundation, reduce risk, and improve your position in the defense supply chain.
Don’t wait for compliance deadlines to take action.
Partner with Techellence to optimize your IT operations, enhance security, and drive sustainable business growth.













.png)











.png)




.png)

.png)
.png)
.png)

